Cyber Fraud Part 7 - SIM Swap / SIM Cloning
Using this method, fraudsters obtain your phone number in order to gain money
Nowadays, cybercrimes occur very often. Many fraudsters extort money from individuals in various ways. Nearly everyone uses a mobile device in today's rapidly developing technological environment. You can access anything with only one click thanks to mobile devices. This article on cybercrime will center on a practice used by fraudsters called Sim Swap/Sim Cloning.
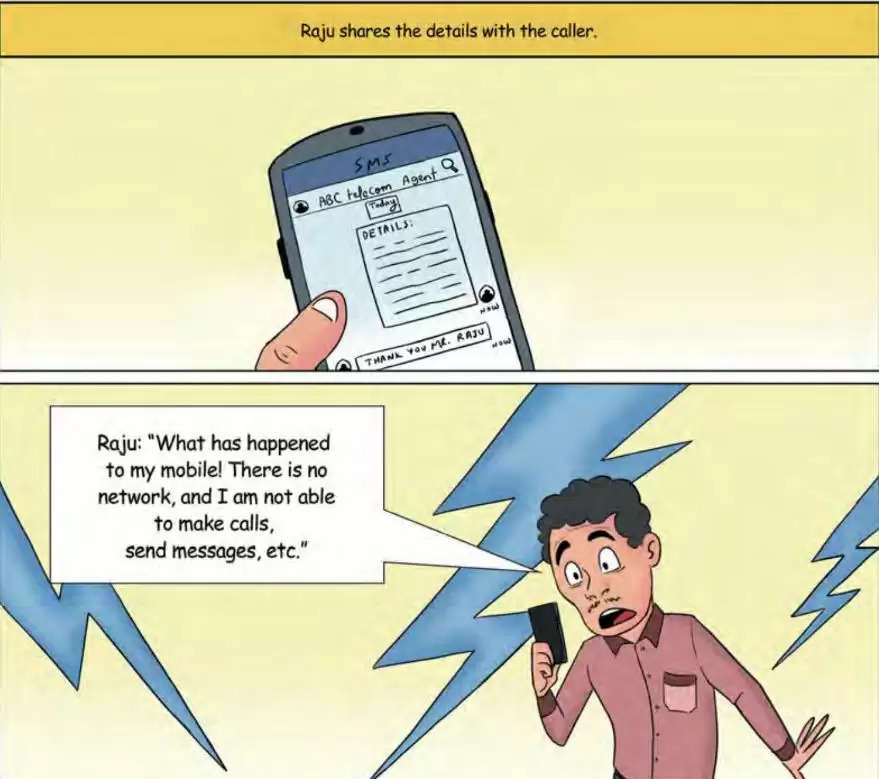
Online fraud can damage your mobile device and take control of your phone number by using SIM Swapping and Cloning. Once the fraudster has control over your mobile device, they may access your OTP, Pin codes, and authentication messages (SMS), which gives them access to your mobile’s sensitive data and allows them to steal money.

How does this fraud technique work?
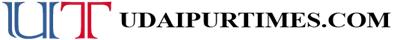
SIM Swap is often called by other terms like sim hijacking and SIM splitting. This happens when scammers or fraudsters identify flaws in the two-factor authentication and verification in which the user gets a message with an OTP (One Time Password) on his mobile phone.
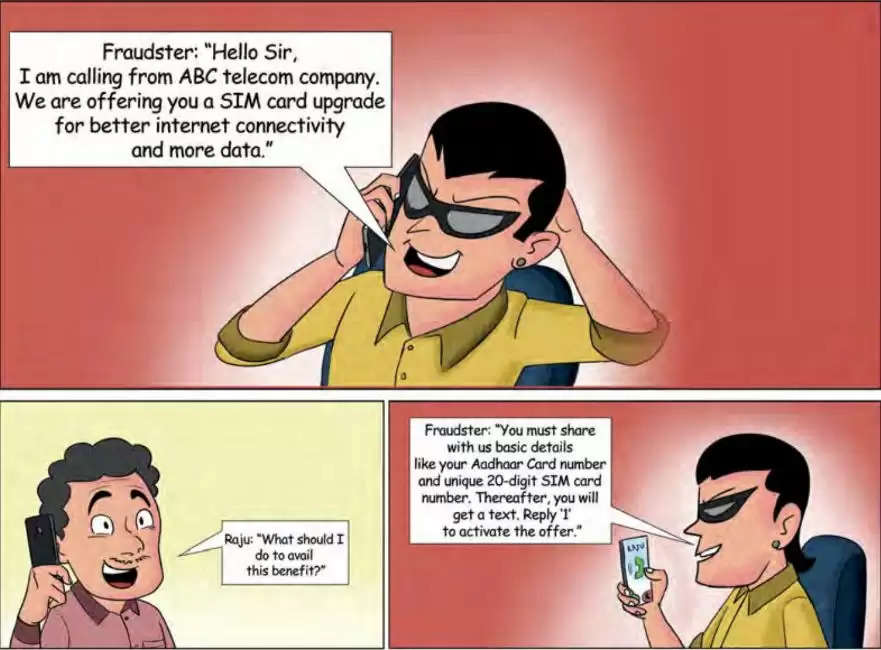
A person's inability to phone or text someone is a clear indication that they are having communication problems. It most likely indicates that the SIM card may have been disabled by scammers. In the event that accessing accounts won't be feasible, getting in touch with the bank should be your top priority. Receiving alerts when your SIM card is activated in another location.
These fraudsters call service providers while posing as someone else, telling them that their SIM card is malfunctioning in various ways. They then request that a fresh SIM card can be activated from customer support.
To access that SIM card and deactivate it, the next step is to call the person they are impersonating and assure them of the same. Once these fraudsters have control over someone's mobile number, they have access to all of their available information, including bank account information and phone contacts. Now that they have complete access to everything a person owns, all they have to do is reset the password for each of them.
SIM Cloning is the process of making an identical SIM from the original. It resembles switching SIM cards. However, this is a highly complex process that copies the genuine SIM card using software. It is done by using Smart Card copying software to create a duplicate of the original SIM.
They gain access to the SIM card's IMSI (International Mobile Subscriber Identity) number during the procedure. They may also use Over- the- air (OTA) connectivity to decode updates received to the SIM through SMS, which would constitute remote hacking.
By cloning the SIM, the fraudster will be able to seize control and use the mobile number to track, monitor, listen to calls, place calls, and send SMS.
How to avoid these scams?
- If in doubt, check the status of the Sim Card with your telecom company's service provider rather than believing the unidentified call.
- Don't give out private information to unknown callers, such as your SIM card number and Aadhaar number.
- Keep an eye on where you input your personal information and email address since they might be phishing efforts designed to trick your bank or cell phone provider into thinking they are you.
- Use strong passwords for every app.
- Use two-factor authentication programmes like Google Authenticator, which sends codes to the app rather than your phone.
- Report the occurrence to the local cybercrime police station and the National Cybercrime Reporting Portal http://cybercrime.gov.in/
Sources: Click Here
To join us on Facebook Click Here and Subscribe to UdaipurTimes Broadcast channels on GoogleNews | Telegram | Signal