Cyber Fraud Part 15 - Fraud Through Email
Beware of anonymous Emails
Criminal action that uses or targets a computer, a computer network, or a networked device is known as cybercrime. The majority of cybercrime is conducted by hackers or cybercriminals who want your money. These could be either personal or political. Cybercrime can be committed by both individuals and groups of people. Some online criminals are well-organized, employ cutting-edge methods, and have extensive technological skills. This article will highlight Fraud Through Email.
Beware of unidentified Emails
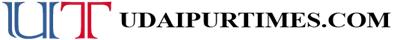
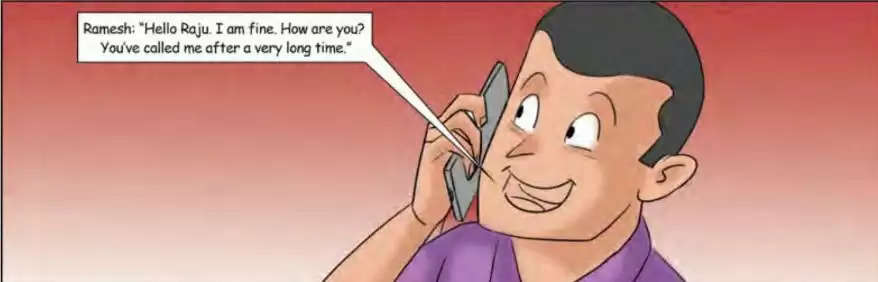
Although email scams are widespread, there are several ways they may be carried out. If a stranger emails you pretending to be one of your acquaintances and requests money and you send them the money without verifying their identification, you have been tricked by scammers. These are called request frauds.
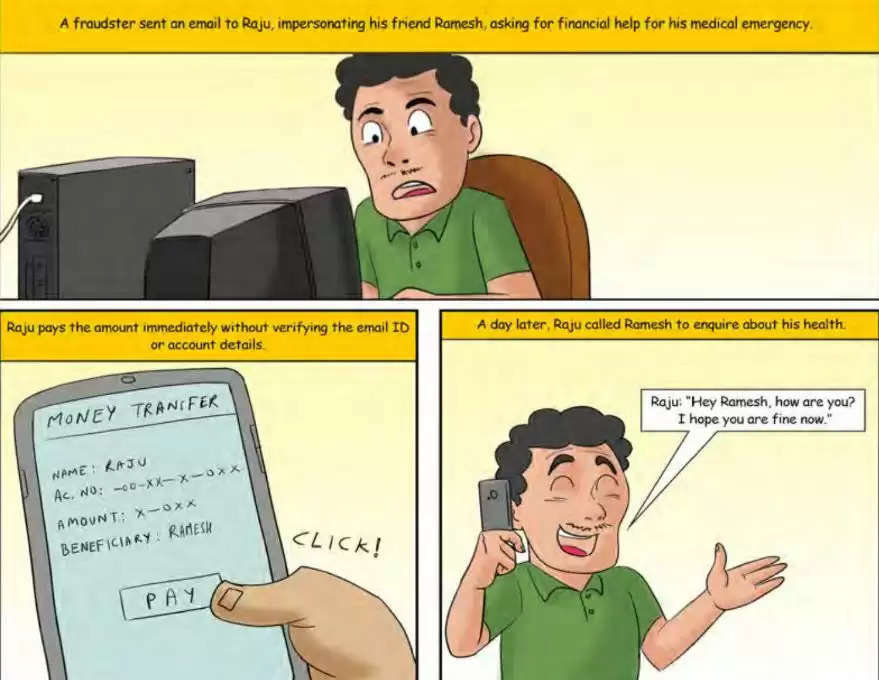
Spoofing is the practice of sending emails from a person claiming to be someone else. Spoofing can happen in a variety of ways. They all have the trait of hiding or masking the sender's identity and the message's source from the receiver.
Email offers to buy products or services might be an example of attempted fraud. A popular item or service is frequently offered fraudulently at a big discount.
Phishing is a sort of social engineering in which an attacker sends a false message intended to dupe a recipient into giving the attacker access to sensitive information. In this case, the "bait" may be a message purporting to be from "the fraud department" of the victim's bank, asking the client to "check their details," "log in to their account," "establish a new password," or other similar requirements. They are led to a page that looks exactly the same but has a different URL rather than the website they trust. The offenders can see the victim's username and password after inputting their log-in information.
Avoid the Scam
- Verify with the person concerned before making any payment based on the email received.
- Verify the Email ID.
- Don’t make payments on receiving requests from random emails or similar- looking email IDs.
- Report the occurrence to the local cybercrime police station and the National Cybercrime Reporting http://cybercrime.gov.in/
Sources: Click Here
To join us on Facebook Click Here and Subscribe to UdaipurTimes Broadcast channels on GoogleNews | Telegram | Signal